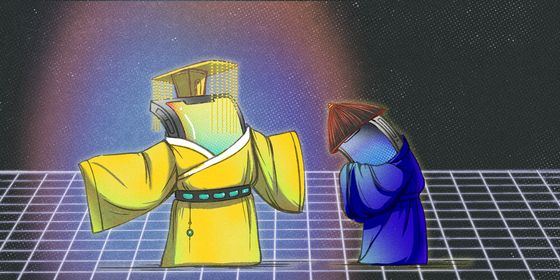
Trolls, anonymous activists, software pirates and foul-mouthed keyboard warriors beware: The government’s coming for your identity.
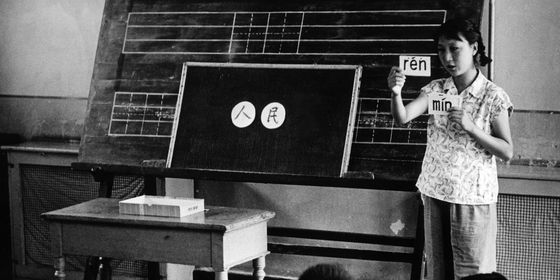
On August 25, the Cyberspace Administration of China (CAC) dropped a bombshell—if you’re capable of being surprised by fresh censorship regulations—by announcing that anonymous comments would be banned on Chinese websites. Though lacking specifics, the order seemed to indicate that those wishing to interact with any Chinese website, anywhere, will need to register their real name and personal details with the site (and by extension the authorities if they ask the site for that information).
If implemented in its entirety, the policy, due to come into effect from October 1, would mean that netizens could still pick a username that masks their identity from other commenters, but the site itself would have access to their information.
It’s not just comment on articles, either. Even danmu, the comments that scroll across streamed videos, are included in the order.
Websites with comment sections will need staff to monitor threads for “illegal content,” but, in appropriately Kafkaesque fashion, website proprietors are also forbidden from distorting the context of discussions by selectively removing or deleting threads. (In similar confused fashion, on Monday Xinhua announced that the authorities are formulating a ban on “improper” use of the national anthem, but will also encourage its use on “proper” occasions, with the lines between appropriate and inappropriate occasions being rather unclear).
It’s difficult to say how far-reaching the ban will be, as enforcement may be patchy and some key areas for online discussion—including Weibo and Wechat—already require registration of ID. But the news comes as the government seems poised to squeeze the last lifeline to overseas sites, namely VPNs. In future, Chinese users will have to register individually for a single-location, state-approved VPN which will “require a list of named individual users, be constantly monitored, and only be allowed to be used for a limited group of approved functions, rather than providing free access to the outside world.”